We Did It! GitProtect.io by Xopero Software Is SOC2 Compliant
“The more efficiently you store your data, the more benefits your business will see” – the great lines said by Thomas Harrer from IBM, that describe the realities of today in the field of data security and data protection. But how can a usual customer understand which company he can entrust his data to and which company needs to be avoided or, at least, questioned?
This crucial measure is SOC 2, which is a set of rules and regulations that has at its aim to reduce the risk and exposure to the data the company stores. And before you even have thought about whether GitProtect.io is SOC 2 Compliant, we want to go ahead and say that definitely YES! We have been thoroughly checked and audited in four categories: Security, Availability, Processing Integrity, and Confidentiality so you can be sure we met all world-class level standards.
As GitProtect.io is a product of Xopero Software, it can surely boast of being reliable and secure as Xopero Software has recently completed its SOC 2 Audit. So, let’s see what we have learned about SOC 2 and what it means for GitProtect.io and our customers.
Why are cloud and third-party providers eager to become SOC 2 Compliant?
We have already mentioned that SOC 2 is a number of requirements and regulations for data security. SOC 2 Audit, which stands for the Service Organization Control 2, was developed and first presented in 2010 by the American Institute of Certified Public Accounts (AICPA). But there is still a question – why is it so important? Data security nowadays is a key point, especially when we speak about source code and Intellectual Property. We all understand that if a company loses its code – it can lose everything if there is no well-built backup & recovery plan.
Under SOC 2 certification AICPA defines five major grounds which each company that stores the data needs to follow. They are:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
All of them became postulates for all respected and honored storage and third-party providers, as they assure the customers that they can rely on the mentioned companies.
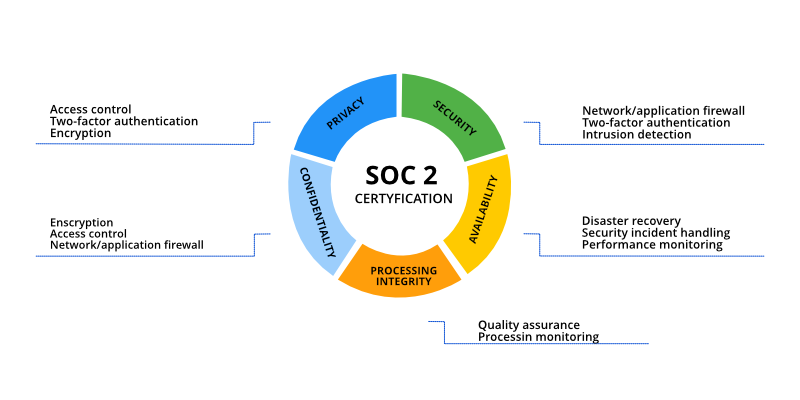
What does Security stand for?
From its name, we can see that Security means all the measures the company takes to eliminate unauthorized access and consequent data breach. They can apply two-factor authentication, network or application firewalls, and any other ways of intrusion detection.
Why Availability is another “pillar”?
If a company announces that it is SOC 2 compliant, it guarantees that the data is available under any external or internal threat. On top of that, they definitely have security incident handling, Disaster Recovery feature, and performance monitoring.
Why does Processing Integrity matter?
It is always great to know that your data is safe, isn’t it? Thus, with Processing Integrity customers can be sure that the company provides full quality assurance and processing monitoring – there isn’t any delay, error, or unauthorized manipulation.
Why does Confidentiality increase companies’ reliability?
Confidentiality is all about data integrity and perseverance. Each company has information, like business plans, intellectual property, or budget documents, which should be kept for some time according to the time limit, depending on the data there can be 5 or 10 years of retention. Thus, it is virtually important to implement access controls and encryption.
Why is Privacy still mentioned?
Under this feature, we understand that all personal information has to be collected and processed according to all the security measures. It means that it will never be disposed of by anybody.
What are our customers granted under GitProtect.io’s SOC 2 Compliance?
First of all, our customers get confidence that our infrastructure, tools, and processes (so your data too!) are resistant to unauthorized access both inside and outside the company and we are ready to mitigate common security risks.
Once the company becomes SOC 2 compliant, it continues to prove that day by day. To get through the Audit, each company should be cross-questioned with numerous checks and, not even should, but, MUST meet all the requirements the SOC 2 covers.
Thus, we guarantee that all our customers’ data is perfectly secured under the following stages:
- Continuous security
- Host-based monitoring
- Alerting procedures
- Audit trails.
The best way to see the benefits the customers have is to look at the table:
| Stage | What GitProtect.io implies | What it gives to our customers |
| Continuous security monitoring | process and procedure practices to monitor unusual system activity, the changes in system configuration from (un)/authorized users, access levels | peace of mind, as we definitely know what happens with our cloud infrastructure and we detect all the potential threats from internal and external sources |
| Alerting procedures | set up alerts for any activities, controls, configurations, logins, and account access against unauthorized data exposure and modification | reliability, as our algorithm prevents data to be compromised or lost |
| Host-based monitoring | procedures and corrective actions, which should be taken in case of outages, disasters, etc. | assurance in a work duration, as incremental, granular, point-in-time, and Disaster Recovery guarantee that you can continue your work without delays |
| Audit trails | the way to understand the root of the problem to decide it as fast as possible | awareness, as you will definitely know when the problem started and how to remedy it |
What does SOC 2 mean for GitProtect.io by Xopero Software?
With SOC 2 Type I Compliance, we understand that our security route has just started (Type II and ISO27K coming soon!). And every day we do our best to improve and increase our customers’ source code protection with the proven secure backup and recovery solution we provide. We realize that the value of the data is growing rapidly from day to day and in the future, it could be even much more valuable than it is now. Thus, we see that no matter how strong your security is, it should be constantly improved and strengthened.
Nowadays we can assure our customers that our solution is the most advanced and reliable, and they can peacefully write their codes, as we provide them with fast and secure automated backup and recovery solutions.